Tailored Business Solution
Have a big idea or objective and need some help? Reach out and see how some of the world's best engineers can take a problem as input and make magic happen.
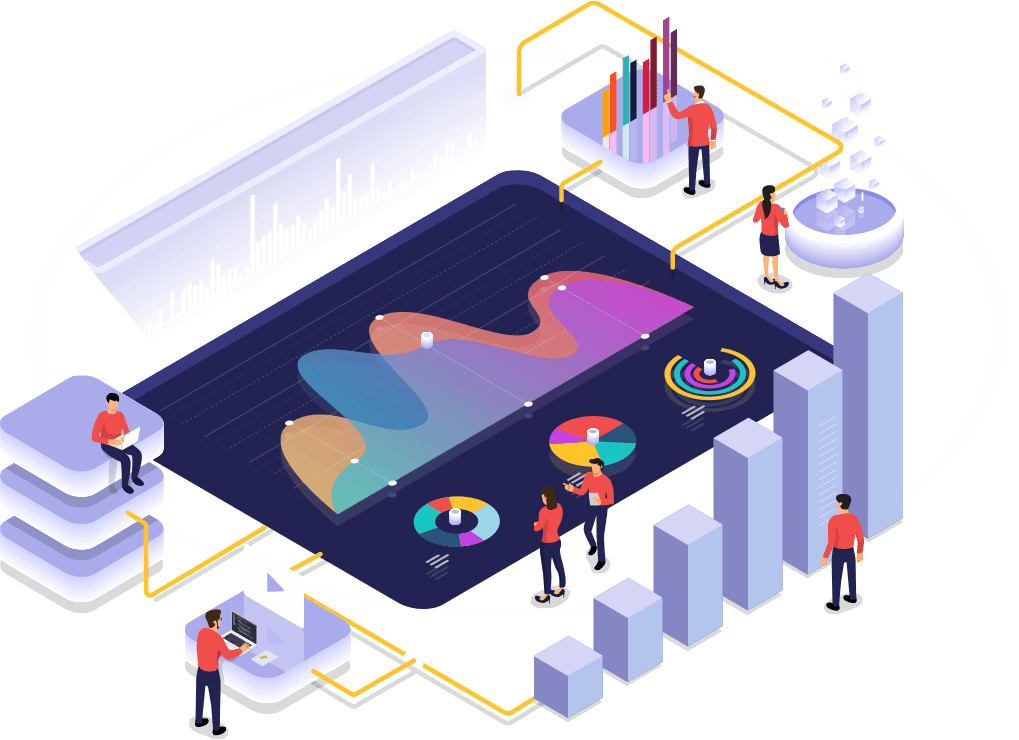
- Web Performance
- Vision AI
- Single SignOn
- Quality Pipeline
- Business Intelligence
- Payment Solutions
We have a lot of experience with companies of all sizes from startups to large enterprises looking to grow their business and need some help. Reach out and see how we can help.
Get In Touch